Kawasaki, Japan, October 22, 2012
Fujitsu Laboratories Limited has developed technologies that protect the privacy of sensor data—such as data from intelligent home appliances and location data—starting from the data collection stage to utilization of the analytic results. Protection of such data is vital, as with its increasing utilization data leaks and other breaches of privacy have become a worrisome social issue.
These technologies consist of: 1) partial decryption technology that takes encrypted sensor data and masks a portion of it, replaces the user ID to an anonymous ID, or converts the encryption key, while maintaining encryption; and 2) anonymous access technology by which users, without divulging their ID to the utilization service, are able to receive their own analytic results from the utilization service.
These technologies enable users to effectively control their private data within the pool of sensor data so that it is safe to use third-party contractors to handle the processing involved in data utilization.
These technologies will be presented at the Computer Security Symposium 2012 (CSS2012), which will be held at KUNIBIKI MESSE (Shimane Prefectural Convention Center) October 30th - November 1st, 2012, sponsored by the Computer Security Group of the Information Processing Society of Japan.
Background
The emergence of the big data era has boosted expectations of a dramatic rise in the collection and utilization of pools of sensor data, such as data from intelligent home appliances, location data, camera monitors and smart meters. Despite a significant amount of data linked to individuals included in these pools, up until now only limited privacy protections have been implemented. Regulations, however, are in the process of being strengthened around the world, as with the EU Data Protection Directive(1). Accordingly, there will be a need to collect and utilize this sensor data while protecting privacy.
Fujitsu Laboratories previously developed and validated data masking technology to enable the secure use of data being transmitted between clouds. Now the application of this technology has been expanded to preserve the privacy of sensor data during collection and utilization.
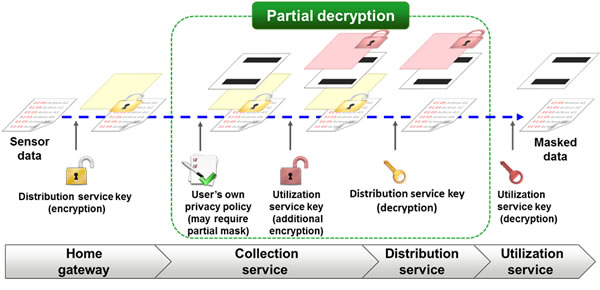
 Figure 1. Example of secure use of sensor data using the new technologies
Figure 1. Example of secure use of sensor data using the new technologies
Technological Issues
Sensor data includes data that identify individuals—user IDs, as well as other sorts of private information, such as the routes people take in transit or whether they are home or not. Accordingly, if these data are linked back to the individuals, all kinds of information about an individual's actions and behavior would become exposed, posing a serious danger. For example, burglars may rob a home if they know the owner is out. Therefore, a need exists for individuals to be able to change their ID in the data and restrict content provided so that only designated service providers can use it.
With conventional encryption technologies, such as SSL communication, users' IDs and data can be protected along the transmission route, but the data is decrypted once the data reach the recipient, making this an inadequate method for protecting privacy. Moreover, for a given set of data, this method does not allow the use ID to be replaced, or the encryption key to be converted for each separate recipient of the data.
The Newly Developed Technology
To resolve these problems, Fujitsu Laboratories developed privacy-protection technologies for sensor data, protecting it from the collection stage to utilization, the first technology of its kind in the world (figure 1). This technology has the following features.
1. Partial Decryption Technology
Partial decryption technology takes encrypted sensor data and enables the masking of a portion of the sensitive data, while also enabling the user IDs to be replaced or encryption keys to be converted, while maintaining encryption. From the time the data leave the home gateway to the time they arrive at the utilization service provider, they never once revert to their raw, unencrypted state (figure 2). With this technology users can for each individual utilization service provider customize the data provision policies of their data by masking a portion of the sensor data or replacing their IDs for the purpose of analytics. In this way, only designated utilization service providers would be able to see the data, enabling individuals' privacy to be preserved.
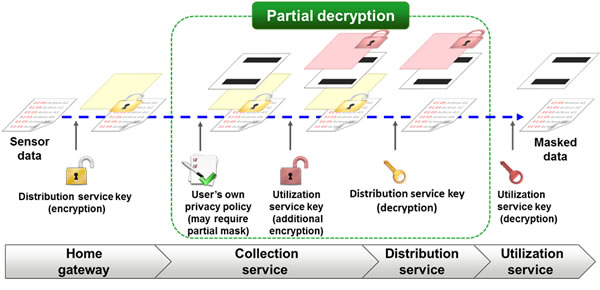 Figure 2. Overview of Partial Decryption Technology
Figure 2. Overview of Partial Decryption Technology
2. Anonymous Access Technology
Anonymous access technology enables users, without divulging their IDs to the utilization service, to receive their own analytic results from the utilization service. When a utilization service provider receives a request from a user (through an anonymous access application) for the analytic results of the sensor data, it issues an access ticket (like the tickets issued by some retailers to determine who is next in line for service). Upon receiving the access ticket, the user then logs onto a distribution service using his or her user ID and provides the information on the access ticket.
The distribution service provider informs the utilization service provider of the anonymous ID for the analytics corresponding to the user ID and the access ticket information. The utilization service provider analyzes the data of the anonymous ID, and then returns the analytic results to the user to whom it had issued the access ticket (figure 3). In this process, because the utilization service is never informed of the user ID, it is unable to identify the individual user, avoiding the risk, for example, that the analytic results could be used to identify houses where no one is home. There is also a benefit to the utilization service in that it avoids the need to manage unnecessary personal data.
 Figure 3. Overview of Anonymous Access Technology
Figure 3. Overview of Anonymous Access Technology
Results
With these technologies, users can control on their own contents of the sensor data they provide and the utilization services to which they wish to provide it. For example, through the use of a smart meter, while keeping all homes anonymous, a household could compare its electricity consumption trends to the average home in its region and optimize the use of electricity within the household. Or, using travel data from automobiles, without identifying individual drivers, it would be possible to analyze areas where it is dangerous to drive.
Future Plans
Fujitsu Laboratories plans to validate the technologies using actual location or other data and, in the future, apply it to network services and cooperative initiatives between multiple cloud services.
![]() E-mail: inquiry_sensordata_privacy@ml.labs.fujitsu.com
E-mail: inquiry_sensordata_privacy@ml.labs.fujitsu.com