Archived content
NOTE: this is an archived page and the content is likely to be out of date.
"Detection" Focused Countermeasures Have Reached Their Limits How to Defend Companies from Intensifying Cyber-attacks
On November 28, 2016, it was reported that t the communications network infrastructure of Japanese Ministry of Defense and Self-Defense Forces was hit by cyber-attack. This is just a part of the current reality of increasing cyber-attacks targeting Japan. Improving cyber security countermeasures is now a national-level issue of the highest importance. What should we do? I asked Mr. Taishu Ohta, an Evangelist at Fujitsu's Cyber Security Business Strategy Unit, who has spent many years engaged in providing support for security countermeasures for Japanese companies, and was also appointed the first head of Fujitsu's Security Initiative Center.
(Interviewer: Tomio Kikyobara, Director at Nikkei BP ICT Innovations Research Institute)

Confidential information is the target -The objective of cyber-attacks is intelligence assessment
-It has been reported that the targeted attack on JTB Corporation on June 2016, disguised itself using the e-mail address of a business partner. One gets the feeling that cyber-attacks are becoming increasingly sophisticated. Would you tell me more about recent trends?
There is a sense that attacker's objectives are becoming more sophisticated, as well as having strong elements of intelligence assessment. The objective of traditional cyber-attacks was to make profit by stealing personal information, and selling them to criminals on the black market.
In contrast, we now have many notable cases suggesting that large organizations on a national scale are mounting attacks as a part of intelligence assessment activities. Most major companies have implemented Security Information and Event Management (SIEM), a mechanism that collects and manages logs from multiple security devices and analyzes the data for correlations. Looking at those results we find a large trend of attackers targeting specific people and stealing the information of leading figures such as company and government officials, instead of regular individuals.
Something else we see is the prevalence of ransomware, malware that infects systems with a virus, restricting access and demanding payment for the release of the systems. Underlying this is a significant drop in the selling price of personal information on the black market. According to a U.S. security vendor, in 2015 the value of one record of personal information was around $25 in 2015. However, in 2016 that dropped to around $6. In other words, stealing and selling personal information has become an inefficient form of business for attackers.
This is most likely the reason for the shift to ransomware, with its high profit margin, and the ability for attackers to set prices themselves.

Taishu Ohta
Evangelist
Cyber Security Business Strategy Unit
Fujitsu Limited
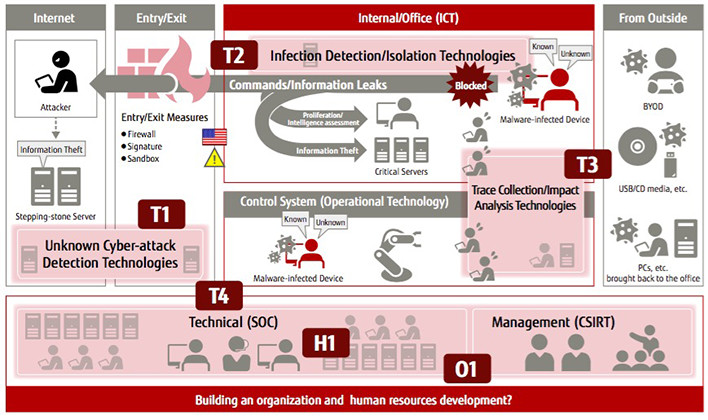 Figure 1: Overview of the security technology being developed by Fujitsu
Figure 1: Overview of the security technology being developed by Fujitsu
-If the objectives of attackers are changing, then management probably needs to reconsider existing security countermeasures.
Until now, management has made its primary objective "information assurance" that prevented information leaks. Going forward, they need to build security countermeasures focusing on "mission assurance" that assures the continuity of business even in the event of a cyber-attack.
In December 2015, the Japanese Ministry of Economy, Trade and Industry released its Cyber Security Management Guideline. Within its "10 Important Items for Cyber Security Management" the Guideline states that there is a need for "proactive countermeasures to prevent cyber-attacks that take risks into account."
In the coming years, cyber-physical systems that tightly link cyberspace with the real world will become more widespread. When this happens, incidents in cyberspace will cause enormous damage to real business. Management needs to recognize that "cyber-attacks are a threat to every aspect of business."
-Are there any characteristics unique to cyber-attacks that are specific to certain businesses or industries?
There is little difference in the attack processes, but attackers' targets do differ by industry. For example, an overwhelming number of attacks against the merchandising industry go after credit card information. On the other hand, we gather that attacks against the manufacturing industry target design drawings and documents containing manufacturing knowhow.
Even though attack processes may be the same, the attack campaigns (a series of continuous attack behaviors starting with the unauthorized intrusion into a network, and finishing with the theft of information or destruction of systems) vary by industry. To respond to them, it is vital that a system be built that can share information over an entire industry, and deal with the attacks proactively.
Countermeasures that prevent "malware from acting even if it gets inside"
-Has there been a change in kinds of cyber-attack countermeasures that companies are requesting compared with previous years?
In fact, not a single issue related to security countermeasures has been solved since the start of the spread of the Internet (from around 2000). Then, as now, the same things were being said: "intrusion and infection by a virus can't be defended against"; "attacker behavior can't be visualized"; "recovering from infection takes a long time"; "technicians handling security countermeasures are inexperienced."
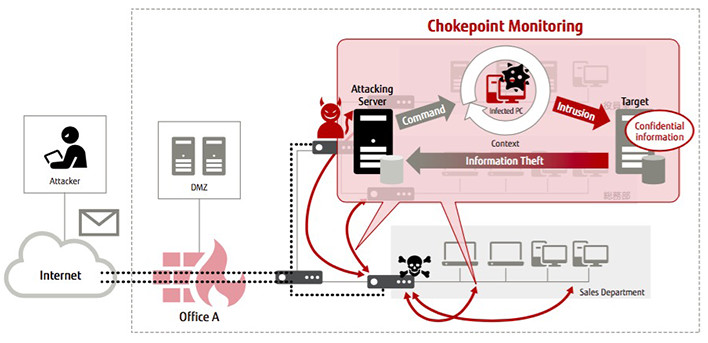 Figure 2: Overview of iNetSec Intra Wall, malware isolation technology
Figure 2: Overview of iNetSec Intra Wall, malware isolation technology
Chokepoint monitoring (for spreading of infections, intelligence assessment activities by remote command) & cut-off
Unfortunately, the situation remains the same today.
Most companies collect and analyze a variety of logs taken from the network and other devices to investigate the damage incurred in an attack by malware that has infiltrated their organization. However, it costs both time and money to gain a complete understanding of the damage done. For example, the approximate cost for forensics that collects and analyzes the electronic data stored on a PC infected by a virus as evidence is said to be around 1 million JPY per PC. There are also methods for gathering the communications logs for an entire network and analyzing them, but these are also very costly.
We are now at the point where security countermeasures placing emphasis on "discovering malware" are reaching their limit. Currently, almost 1 million types of new malware (including variants) are released every day, yet the detection rate for these by pattern matching is less than 50%. Malware slips through or gets missed and defense against it is falling behind because of this. I think that we need to conscious of the fact that building a system that can completely prevent malware intrusions and information leaks is impossible.
What companies need now are countermeasures that presume intrusion by malware, can identify the malware that has infiltrated the organization's network, and visualize the behaviors of the malware.
The companies then needs to monitor chokepoints (points where communications must pass through) for remote commands from the C&C (Command & Control) server, preventing viruss from acting even if it does infiltrate the network.
An "Attacker Behavioral-Transition Model" built on observations of the behavioral processes of attackers
-What security technologies is Fujitsu focusing to neutralize malware activity?
For companies working on security countermeasures, they must select and utilize technologies appropriate to the countermeasure's objectives, which is far from easy to do.
In response to this, Fujitsu is developing security technology divided into four areas, T1-T4 (Fig.1). T1 consists of security countermeasures for entry and exit points. Usually, indications of a targeted attack are detected using sandboxing, firewalls and signature-based approaches, however these are not enough. We have developed a new technology called "Malicious Intrusion Process Scan" that focuses on the behavioral processes of attackers.
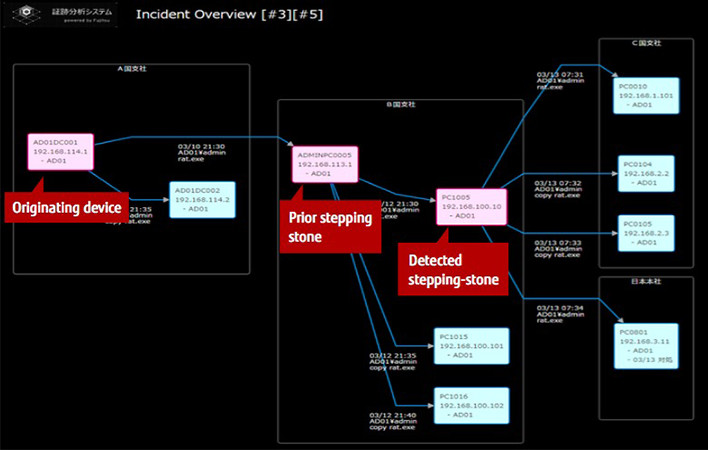 Figure 3: Bird's-eye view that provides an understanding of the status of an attack
Figure 3: Bird's-eye view that provides an understanding of the status of an attack
It detects an attacker's activities in real time by comparing the flow of attack behaviors with the model (an attacker behavior-transition model) which was build based on the observed behavior of attackers that have penetrated organizations in the past.
-So you focused on the attacker, and not the malware itself.
That's right. Regardless of the size of an attack or the type of information stolen, the processes involved in stealing information through targeted attacks are similar in many ways. It generally begins with a scam e-mailwith a UR is sent that the recipient is made to click, which downloads the malware. Once it is on the PC, the malware spreads itself to other PCs and remote commands from a C&C server are used to listen in on the network to steal information from organization.
Fujitsu's Malicious Intrusion Process Scan monitors the communications of the PC that received the targeted e-mail, and detects an attack by fitting a string of activities, from intrusion behaviors to information theft activities, to the attacker behavioral-transition model. Constant monitoring of PCs immediately after they are infected provides an understanding of an attacker's behavior in real time, and increases the accuracy of detection.
The next area, T2 uses technology called iNetSec Intra Wall to isolate malware that has already penetrated into the organization's system. The device monitors network traffic, detects malware activity in real time, and automatically isolates infected devices. This is effective in detecting the location of unknown malware as the technology evaluates the behavior of communications common to targeted attacks (Fig.2).
Proprietary Technology Instantly Creates a Full Picture of a Cyber-attack
-For major companies and organizations, there is also the possibility of a malware infection on a single device causing immense damage. In the directed attack against the Japan Pension Service that occurred in 2015, the personal data of more than one million people was leaked, and it took nearly three months to obtain full picture of the attack.
"Performing forensics at a low cost and in a short amount of time" is a big challenge for us. The T3 area offers new trace collection and impact analysis technologies. We have developed high-speed forensic technology that automatically parses massive amounts of network communications, analyzes them, and shows a complete picture of the execution process and the state of a targeted attack in a short amount of time. This technology itself consists of the trace collection and attack progress status extraction technologies.
The trace collection technology captures network packets, inferring the commands performed on the infected PC from their content. It then creates a trace log of executed commands worked out by analyzing the communications between the infected PC and PC being attacked.
Next the attack progress status extraction technology analyzes the trace log (command operations), instantly determining whether those communications have a high probability of being an attack.
Something that should be mentioned about Fujitsu's high-speed forensics technology is that it can show the relationships between devices in an attack in the form of a daisy chain. For example, by analyzing the command operations of a device used as a stepping stone, you can instantly find the prior device used as a stepping stone, and as you go up the chain, you can discover the originating device (Fig. 3). By visualizing this you can render a bird's-eye view of the attack, which provides an understanding of every aspect of it at a glance. Incidentally, this technology could create a general correlation diagram of the targeted attack against the Japan Pension Service in an hour.
-That is some amazing technology.
Our customers often give us the same response. Companies who introduce this technology can do what forensics specialists do in much less time. It has been noted that Japan is lacking 100,000 security engineers, but we believe that our technology can resolve this issue.
The final area, T4, consists of information sharing technologies. Fujitsu has built a "Cyber Threat Intelligence (CTI) Utilization System" that efficiently shares and makes use of cyber threat intelligence. The system puts the 5W1H of a cyber-attack (attacker, time, objectives, attack targets, intrusion routes & method, etc.) and the information for dealing with it in a format that computer can handle.
We built this system so that threat information could be systematically interpreted and shared without involving people. We are now in an era where there is too much threat information for humans to evaluate;this technology aims torealize this decision by machine-to-machine.

-Will these technologies change the current dominant position of attackers?
We hope so. Our biggest fear is this technology falling into their hands. Before they strike, attackers will buy up every existing cyber security product on the market, and study their designs and the technologies used to come up with their own "technology" to circumvent them. We need to take measures to prevent that from happening.
Responding to Unanticipated Events With "OODA Loop"
-How should companies respond when they are the victim of a cyber-attack?
Cyber-attacks are just like a disaster. In other words, they need to be thought about from stance of what needs to be done to get business back up and running as soon as possible after they happen. Companies need to base their perspectives on mission assurance and business continuity, and make it their number one priority to think about how to reduce the length of interruptions and quickly return to normal operations.
To do this, it is essential that companies build a system that can handle unanticipated events even before the next one occurs. I believe it will be vital to for companies to establish an "Observe, Orient, Decide, Act (OODA) Loop" separately from the "Plan, Do, Check, Action (PDCA) Cycle" that they have used until now.
The OODA loop is a model that links in real time cycles of active and continuous observation of changing circumstances, orientation to those circumstances, rapid decision-making, and response. Let's try applying this to security intrusions. Even at the stage where we do not know who the attacker is, and do not have a full picture of the damage done, we can actively "observe" the changing circumstances, "orient" ourselves based on the information available, and having made a "decision" about how to respond, we "act." While the Computer Security Incident Response Team (CSIRT) is the group responsible for the observation and orientation phases, the decision phase is management's job.
Many companies are currently making use of the OODA loop as a crisis management response, however not as a security countermeasure. The rapid detection of trouble, prompt situational judgement and decision-making are important to countermeasures, and I believe that from now companies should make constant use of the OODA loop.
-Security solutions play a major role, don't they?
Fujitsu offers technologies that realize real time "observation" and appropriate "orientation" of the OODA loop. We also perform consulting services that improve crisis management skills, and global management services that support operations. These solutions support companies in rapid "decisions making" which we are convinced serve to strengthen their competitiveness.
* This content appeared on ITpro Active in January 2017.