Introduction of Fujitsu The Netherlands
Fujitsu is a global information and communication technology (ICT) company, offering a full range of technology products, solutions and services. Fujitsu employs over 400 people in The Netherlands, supported by approximately 132,000 colleagues worldwide in 100 countries. We are a dedicated partner for companies that want to take advantage of the opportunities offered by new technology and digitalization to become more efficient and innovative. Not only this, but our people live and breathe our global purpose to make the world more sustainable by building trust in society through innovation - that's about seeing the value technology can create for customers today and in the future - and making it real.
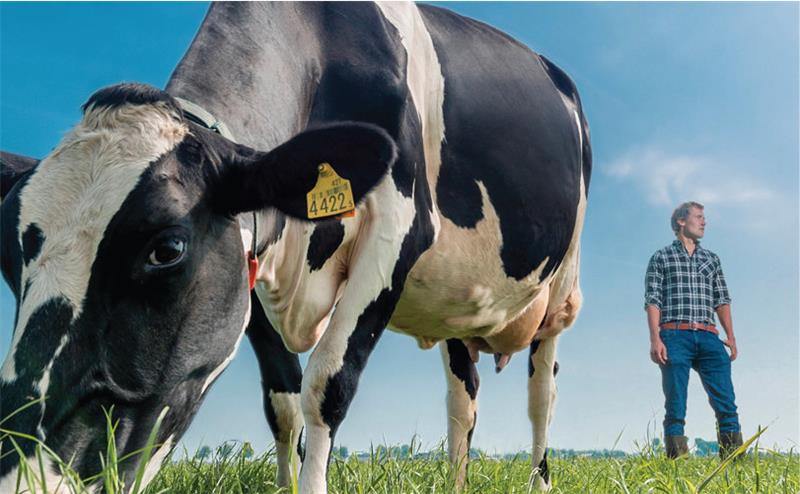
In The Netherlands, we work across the public and private sector including financial services, utilities, and manufacturing. The customers we work with in the region include municipality of North-Holland, Belastingdienst, Robeco, Asics and Royal IHC.