Archived content
NOTE: this is an archived page and the content is likely to be out of date.
FUJITSU Network Virtuora TC
Features of FUJITSU Network Virtuora TC
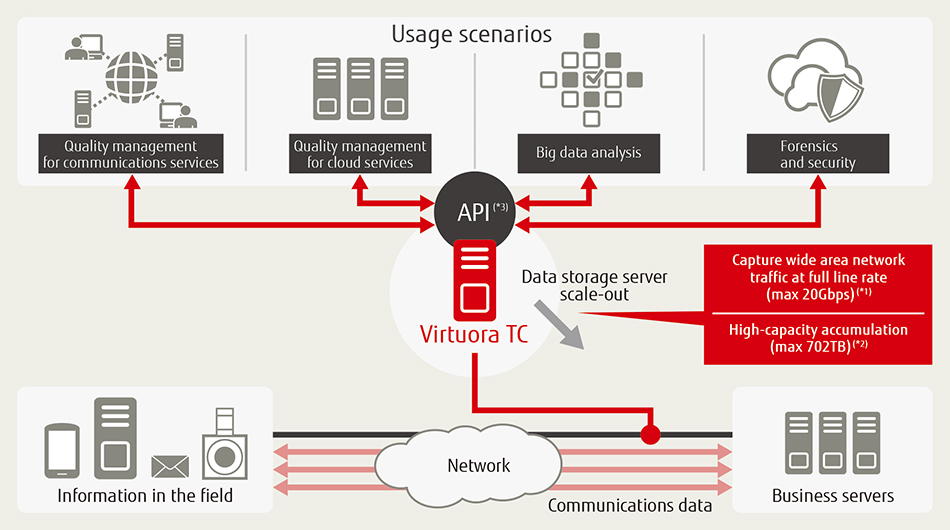
- Virtuora TC is software that can capture up to 20Gbps of network traffic data at full line rate, accumulate data and simultaneously undertake high-speed searching. It enables complete communications data-trail management through high-speed searching for required information from the data accumulated.
- The accumulated communications data can be used by various analysis systems, such as those that manage the quality of communications lines and cloud services, or for security and other purposes, through the API provided by Virtuora TC.
(*1) It can capture up to 10Gbps of network traffic data (total wire speed is 20Gbps, including up-link and down-link) at full line rate.
(*2) When 10Gbps network traffic data (total wire speed of 20Gbps, including up-link and down-link) is flowing at peak network capacity, around three days' worth of network traffic data can be accumulated for the communications data trail. When the upper limit is reached, the oldest data is automatically deleted first.
(*3) It can use the accumulated network traffic data in the form of pcap (packet capture) via a web-based API.
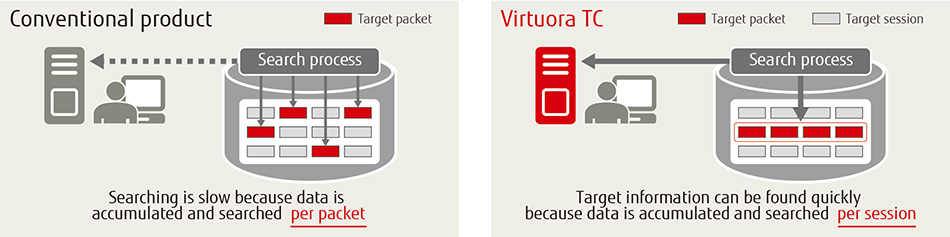
Reduced data analysis time
It typically takes half a day or more to search for the required information from the huge volume of network traffic data. However, Virtuora TC creates indexes for each session, enabling the required information to be found in a few seconds or less than a minute. This significantly reduces the time required for data analysis.
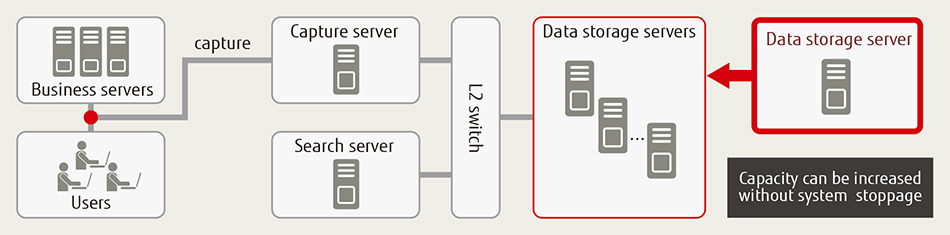
Scalable data accumulation capacity without system stoppage
Virtuora TC makes it possible to increase data accumulation capacity without system stoppage. Therefore, data storage(*4) can be added without losing any network traffic data.
(*4) Up to a maximum of 36 data storage servers can be used.
Minimal initial capital expenditure
With conventional systems, expensive dedicated equipment is required to capture network traffic data from a broadband network at full line rate. Fujitsu has developed Virtuora TC as a software offering bundled with a versatile server. This solution can therefore reduce the capital expenditure outlays typically needed to deploy a network quality management system.
Usage Scenarios
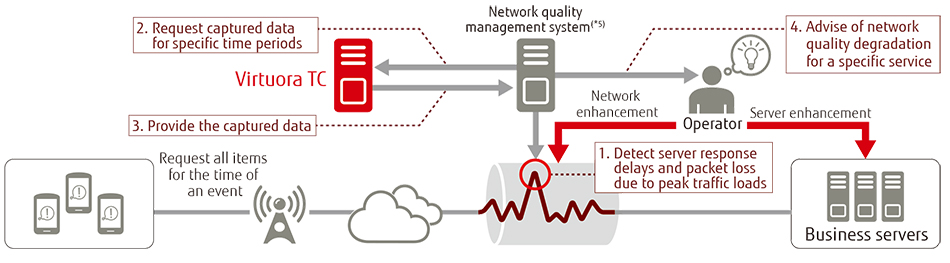
The following usage scenarios resulted from implementing the Virtuora TC network quality management system in customer networks.
1) System enhancement for traffic data increases
In conjunction with the network quality management system, Virtuora TC can analyze the traffic data in detail and find the target information in a few seconds or less than a minute. Virtuora TC assists network operators with faster decision making to dramatically enhance server and network capacity.
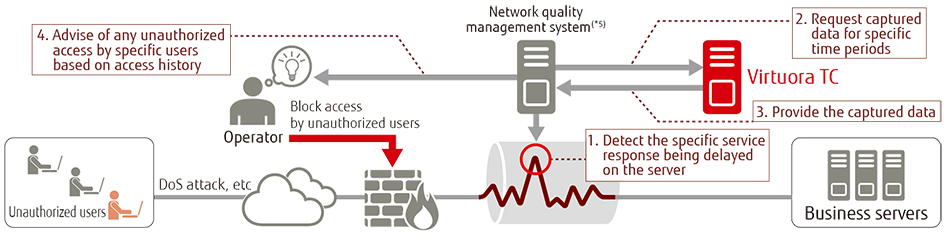
2) Blocking unauthorized access
Events such as DoS (denial of service) attacks, enabled by unauthorized access, can bring down MVNO and ISP web services. Virtuora TC can analyze unauthorized access based on the access history information it gathers on every user's activities. The operator can then block any unauthorized user.
(*5) Network operations can be enhanced by deploying together with FUJITSU Network Proactnes II QM – network quality management software.
Summary of Requirements
Capture Server
| Hardware | CPU | Intel®Xeon® Processor E5-2667v3 (3.20GHz/20MB/8core) ×2 or higher |
|---|---|---|
| Memory | 192GB or higher | |
| Disk | 300GB or higher | |
| Ethernet Card | Dual port LAN card (10GBASE) ×3 or higher | |
| OS | Red Hat Enterprise Linux 6.5 (for Intel64) | |
Data Storage Server
| Hardware | CPU | Intel Xeon Processor E5-2430v2 (2.5GHz/15MB/6core) ×1 or higher |
|---|---|---|
| Memory | 64GB or higher | |
| Disk | SATA Disk (4TB) ×12 | |
| Ethernet Card | Dual port LAN card (10GBASE) ×1 or higher | |
| OS | Red Hat Enterprise Linux 6.5 (for Intel64) | |
Search Server
| Hardware | CPU | Intel Xeon Processor E3-1231v3 (3.40GHz/8MB/4core) ×1 or higher |
|---|---|---|
| Memory | 64GB or higher | |
| Disk | 1TB or higher | |
| Ethernet Card | Dual port LAN card (10GBASE) ×1 or higher | |
| OS | Red Hat Enterprise Linux 6.5 (for Intel64) | |
L2 Switch
| Port numbers | 1000BASE-T | 1 port or higher |
|---|---|---|
| 10GE | 24 ports or higher | |
| Performance | Switch bandwidth | 30Gbps or higher |
| Forwarding rate | 10 million pps or higher |
- Intel and Intel Xeon are trademarks or registered trademarks of Intel Corporation in the United States and/or other countries.
- Ethernet is a trademark or registered trademark of Xerox.
- Linux is a trademark or registered trademark of Linus Torvalds.
- Red Hat and Red Hat Enterprise Linux are trademarks or registered trademarks of Red Hat Inc., registered in the United States and/or other countries.
- All company names, brand names, and product names are trademarks or registered trademarks of their respective holders. The information here is subject to change without notice.
Documentation
- FUJITSU Network Virtuora TC (222 KB)